The Automotive Cybersecurity Industry and Its Unique Challenges
Over the last decade, automobiles have seen an unprecedented level of growth in their connectivity and autonomy capabilities. Traditional vehicle electronic networks and systems that were once housed in iron cages on wheels are now exposed to the outside world through inclusion of Bluetooth, Wi-Fi, and 4G cellular connectivity. This reality has propelled the automotive industry into a new era where vehicles can have their control arrested from their drivers and placed into the hands of a malicious hacker intent on causing damage. This damage can take the form of personal information compromise, automotive ransomware locking a vehicle down until its owner has paid a hefty sum in bitcoin, cyber-terrorism, or targeted assassinations made to look like tragic accidents. The reality is that vehicles are now – and will increasingly become – targets for hackers and cyber criminals all around the world. The full extent to which a vehicle hack can affect a car’s operation was shown in 2015 when two hackers famously took remote control of a Jeep Cherokee from hundreds of kilometers away – without ever physically touching the vehicle. Since their exploits brought automotive cybersecurity into the spotlight, public awareness of the issue and increased attention from the security industry have led to more research showing the sorry state of cybersecurity in the transportation industry. New vulnerabilities are constantly disclosed, highlighting how unprepared vehicles with advanced connectivity and autonomy features are for withstanding the cyber landscape.
The Global Response
To protect the next generation of vehicles, the world has seen a rise in legislation and industry standards tasked with mandating the inclusion of vehicle cybersecurity tests and management systems in vehicle safety approval processes. Key examples of such regulations include the ISO/SAE DIS 21434 (Road Vehicles – Cybersecurity Engineering) industry standard and the recently ratified United Nations ECE WP 29 (Automotive Cybersecurity Regulation). The standards set in place have propelled automotive OEMs and suppliers to begin prioritizing cybersecurity testing for new vehicles and vehicle subsystems. Under UN ECE WP 29, vehicles that have not been granted cybersecurity approval cannot be sold in countries choosing to implement the regulation. This includes major automotive markets such as Japan, the United Kingdom, Russia, Australia, and most of the EU. While the regulation is not directly aimed at suppliers – placing the majority of the burden on the OEMs – it remains true that OEMs now prefer to do business with suppliers that prioritize the implementing of security in their products. Suppliers will soon find themselves ostracized by the greater industry if they fail to meet the cybersecurity sophistication demands set in place by industry and new legislation.
Rapidly Expanding Market, Insufficient Talent Resources
Despite the rising urgency for security in vehicles, the talent pool is, unfortunately, very lacking. Endemic of an industry rising to such importance – essentially overnight – the number of qualified, experienced automotive cybersecurity professionals is too low to ensure that every supplier or OEM has a well-equipped security team. Universities and other institutions of higher learning are not yet equipped with curriculum to reliably produce enough qualified professionals. In an ideal world, cyber criminals would resist targeting vehicles with cyber-attacks until the vehicles are sufficiently prepared to handle and react to their assaults, but the real world is no such place – the industry needs to act now, and society will suffer if the precautions taken are not adequate. Due to the potentially destructive consequences of a vehicle cyber-attack, automotive cybersecurity can, and should, be a concern for all – not just industry and governments. To prevent the advanced connected vehicles of tomorrow from becoming deadly missiles in the hands of a hacker, all members of the automotive ecosystem should take the necessary steps to ensuring their readiness for the future of vehicular cyber-crime.
Ever-Evolving Threat Landscape

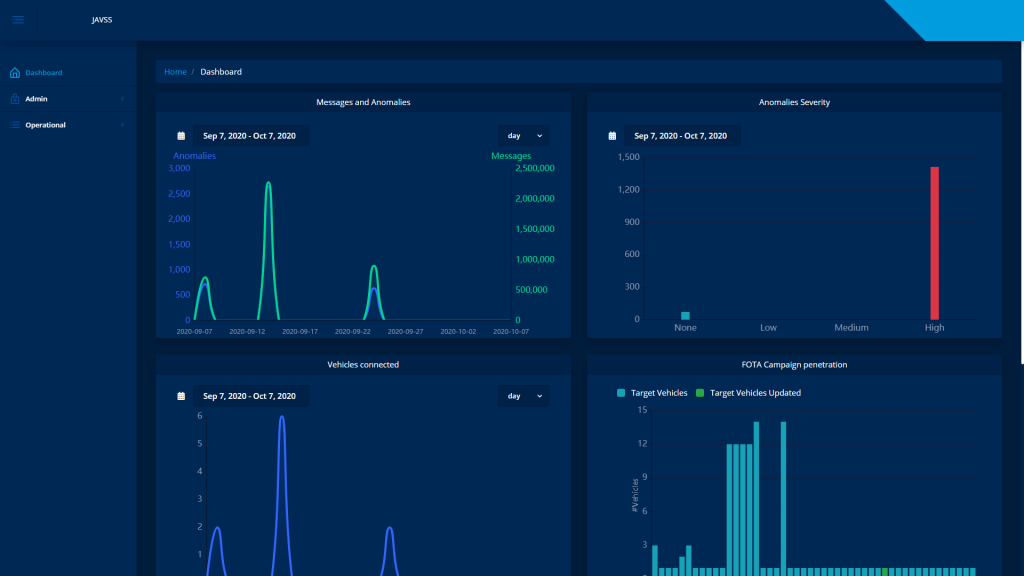
Traditionally, cybersecurity has been a field that demands constant vigilance. New threats and vulnerabilities emerge nearly daily, and the security systems that protect the world’s networks and infrastructure require constant upkeep to remain effective. The same principle applies to automotive security while also introducing new challenges – automobiles have not traditionally been connected to the internet and have thus had to be recalled or brought into a shop to update their software. This is becoming less true as Over-the-Air (OTA) updates make their way into the design of modern vehicles but managing said OTA updates in a secure fashion is its own unique challenge. Updates need to be tested before deployment and signature checks need to be performed before installation on the vehicle to ensure no rogue software makes its way onto the in-vehicle components. These technical demands have led to the birth of the Automotive Security Operations Center (A-SoC) – a specialized platform for monitoring the cyber-health of a fleet of vehicles and securely administering software updates and patches when needed. An example of such is the Joint Anti Vehicle Striking System (JAVSS) developed by White Motion – a state-of-the-art A-SoC platform that leverages vehicle connectivity and a robust public key infrastructure to securely monitor and protect vehicles from cyber-attacks. Vehicle network anomalies are detected an embedded intrusion detection system and uploaded to the JAVSS backend, allowing for remote fleet cybersecurity management, OTA administration, and in-depth incident analysis. Flexible solutions such as the ones JAVSS provides will become increasingly necessary for ensuring the continued safety and security of the next generation of vehicles.
Summary
The rise of connected and autonomous vehicles promises many benefits to both society and the environment, but the risks of approaching such an interconnected future unprepared are tremendous. Automakers and the suppliers they work with need to give cybersecurity preparedness the priority it deserves. Due to the real-world threat vehicle hacking poses to the lives and livelihoods of a vehicle’s passengers, a reactive approach to security is inappropriate – there is no time to waste. In the face of this uncertain future, firms like White Motion are helping the automotive industry prepare itself through developing dedicated cybersecurity products, training customers to bolster human resources, and sharing knowledge and expertise with the industry as a whole. A secure, connected future demands continuous effort from industry , academia, and government. Without the cooperation of every party involved, such a future will forever remain an unobtainable dream.
Author:
Kamel Ghali is an Automotive Cybersecurity Architect at White Motion – subsidiary of the global supplier Marelli. Kamel has excelled in the automotive security industry for over 3 years as an expert car hacker, trainer, and contributor to industry-focused communities worldwide including the SAE and ASRG. At White Motion, Kamel heads the vehicle security research team, assessing vehicle systems and training customers in state-of-the-art car- hacking techniques.
Published in Telematics Wire